Password Security
CellarTracker embraces industry best practices with regard to password handling, cookies, secure web protocols, password reset mechanisms, etc. If you are not especially technical, you can probably stop reading right now. However, if you are in fact much more curious or have specific technical concerns or issues, the goal of this topic is to very transparently disclose our practices in this regard.
Please also read about Privacy Settings for controlling who can see your cellar data as well as our Privacy Policy.
In this article
Technical Details
This section describes in more detail about web protocols (HTTP/HTTPS), SSL/TLS certificates, Cookies, password hashing and general password retention and transmission practices.
HTTPS Details
Traditionally websites have used a secure ( HTTP Secure or HTTPS) page just for initial log-in and then resume the rest of the browsing session over an insecure HTTP connection. However, with the advent of shared, public, wireless access points, this is increasingly problematic as demonstrated by the public release of Firesheep. In short, this partially secure approach makes it easy for anyone to steal your credentials and masquerade as you. As such, CellarTracker has chosen to use HTTPS for ALL browsing for logged in users. While this does induce some extra latency and server expenditures, it is the only proper way to truly protect your information.
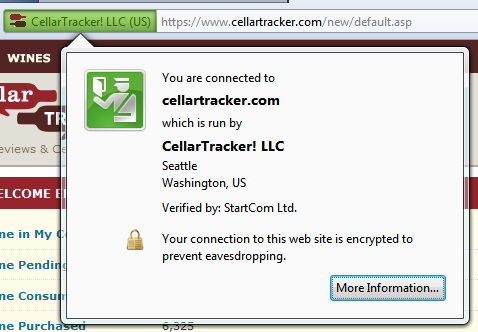
Not all SSL/TLS certificates are created equal. CellarTracker has obtained a Class 4 or Extended Validation (EV) certificate, so CellarTracker will appear green in the browser bar if you are on a secure connection. We have also moved to a SHA256 based certificate, and require TLS 1.0 or higher to use the site via SSL.
Cookie Details
As in keeping with industry best practice, authentication cookies (username and hashed password) generated by CellarTracker are marked as Secure, so they are only transported over HTTPS. The site also marks all cookies as HttpOnly to help mitigate against Cross Site Scripting attacks in mainstream browsers.
Password Security
CellarTracker no longer retains the actual text of any password. Rather your password is securely salted and hashed and only stored in this form. Because of this, passwords are now case sensitive. All formerly retained passwords have been deleted, and site administrators no longer have access to your actual password. If you do forget your password, the site allows you to send a temporary password reset request to your email address of record. Since CellarTracker is not a banking or transactional site, we do not use biometric questions (e.g. what is your dog's name or your mother's maiden name) to further guard password resets. If your email is hijacked, you likely have far bigger concerns than unauthorized access to your CellarTracker account. However, CellarTracker cannot be used as a vector to determine your password so that a hacker can then access your bank accounts on another website.
If for some reason you no longer have access to an old email address that you used on CellarTracker, please send email to support@cellartracker.com with your old email address, your full name, the handle in use on your account, and any other information required to verify your identity. Assuming everything checks out, we will update your email address and send you a password reset request.
Minimum System Requirements
In order to access CellarTracker as a logged in user, your system must be able to support TLS v1.0 or higher and SHA256. The following operating systems are all supported:
- Windows Vista, 7, 8, 8.1+
- Windows XP SP3+ (you MUST have SP3 installed; prior versions will not work)
- Mac OS X 10.5+
- Apple iOS 3+
- Android 2.3+
- Windows Phone 7+
If you're getting an error loading the log-in page, most likely you only have the older, insecure SSLv3 protocol enabled on your device. For Windows/Internet Explorer users: Follow the instructions to disable SSLv3, and also ensure that TLS 1.0, TLS 1.1, and TLS 1.2 are all checked on the same dialog. For all other OSes and Browsers, ensure you meet the minimum requirements above, and are using the latest available version of your browser. Still can't login? Please contact us for additional support.
Using 3rd party Apps
Some 3rd party apps, such as Corkz and VinoPal, interface with CellarTracker via a private API. CellarTracker does not currently implement OAuth 2.0 or some other mechanism to grant access to your CellarTracker account to these applications. We are certainly considering that for the future, but for now we have made some minor upgrades to our API so that these applications will not need to retain your password. There is now a Credentials API that can be passed a handle and password and in return receive a valid password hash. Both VinoPal and Cor.kz have been using this for several years. Also, the current/latest version of Cor.kz has already switched over to HTTPS for all calls to CellarTracker. If you have concerns about this, we either recommend not using these applications or using a special password just for CellarTracker, Cor.kz and VinoPal that is DIFFERENT from passwords that you using for banking and other transactional accounts.
A Note on Credit Card Security
We have made a very conscious decision from day 1 to NEVER store or even handle cardholder data. All payments to CellarTracker come via a drop-in form hosted by Braintree Gateway as part of the Braintree Payments service. This is a 3rd party payment service owned by PapPal. All cardholder data that you enter is handled only by PayPal. We never have access to complete credit card details, and we don't want it. (PCI compliance is a real pain in the neck, and touching credit cards is akin to playing with munitions.)
